Building Reliable Access Systems Through ISP Proxy Infrastructure
Time is money! But do you know you may save both with optimized access control? By building reliable access systems with ISP proxy infrastructure. This involves several things. One, you have to choose the right proxy type. Secondly, you might want to implement proper security measures. Ensuring stable performance is also important.
You may easily do this by leveraging ISP-provided addresses. They play an important role in creating fast, consistent, and resilient connections. ISP proxies combine the high speed of performance of data center proxies and the legitimacy of residential IPs. The results? Systems that are good at evading blocks and reducing latency — maintaining long-term session stability while at it.
Understanding ISP Proxy Infrastructure
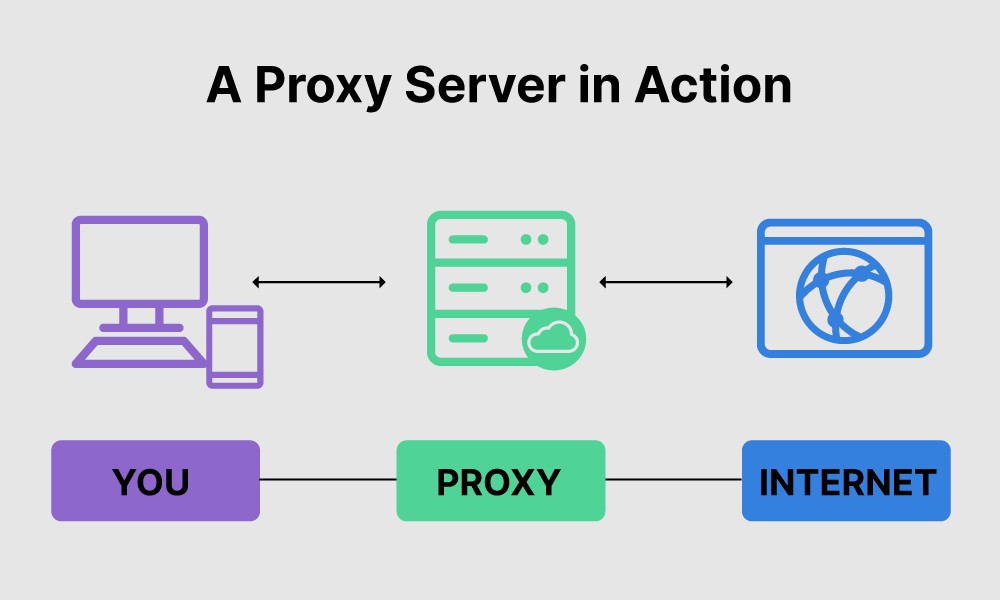
Typically, ISP proxies are hosted in a data center. However, they use IP addresses that the average Internet Service Provider (ISP) would offer. This makes them appear like regular residential users.
These types of proxies combine the speed and reliability of data center proxies. Furthermore, they expertly bring the authority and anonymity of residential proxies into the mix.
The Benefits of ISP Proxies
Much like other types of proxies, ISP proxies have numerous benefits. The most relevant include but are not limited to:
- High reliability and speed: ISP proxies may deliver the low latency and high throughput of data centers. This makes them best for time-sensitive operations. For example, e-commerce price monitoring and ad verification.
- Enhanced anonymity:These proxies may blend in with normal residential traffic. They simply utilize IP ranges assigned by ISPs, which is helpful in reducing the risk of detection and blocking.
- Session stability:Static/semi-static ISP IPs allow for stable sessions. This may be important for tasks requiring long-lived authentication or complex workflows.
- Global coverage:Leading ISP proxy providers offer extensive geolocation options. This may enable you to access region-specific content reliably.
Designing Reliable Access Systems
There are several actors that may be helpful in building reliable access systems through ISP proxy infrastructure. These may involve defining objectives and requirements and setting clear metrics. To achieve this, you must create a catalog of your use cases. For example:
- Web scraping volume
- Geo-targeting granularity
- Throughput needs
- Compliance mandates
ISP Proxies Infrastructure Architecture
This refers to the design and setup of proxy systems that use Internet Service Provider IP addresses to route internet traffic. The infrastructure architecture behind ISP proxies usually considers three elements:
- Provider vs. self-hosted: There are several things you may evaluate. You may purchase ISP proxy services from established vendors. Or, lease static IPs directly from ISPs and self-host your proxy servers.
- Isolate in a DMZ:Place proxies in a demilitarized zone. This may shield your core network. Also, it may grant controlled external access.
- Load balance and fail-over: Deploy edge load balancers and dual-ISP links. Furthermore, configure health checks that switch traffic to backups instantly if a proxy fails.
Implementation Strategies
Implementing ISP proxies effectively requires more than just picking a vendor and plugging in IPs. You need a strategic approach to provider selection, deployment, and scaling to ensure reliability, security, and performance.
Pick the Right Provider
Evaluate vendors on SLAs. You may aim for
- A 99.9% uptime or higher availability
- Generous bandwidth (to prevent throttling)
- Broad geographic IP pools
- Strong security practices (TLS encryption, minimal logging)
Deploy with Best Practices
Rotate proxy IPs within defined session windows. This may help keep sessions persistent and avoid blocks. You may use proxies with built-in edge DNS resolution for latency-sensitive traffic.
Set up health checks at both application and network layers. This may trigger automatic switchover to backup proxies upon failure. Lastly, run proxy servers in containers or elastic cloud instances. This may help you add capacity on demand.
Security and Privacy
To secure proxy access and prevent unauthorized usage, you must encrypt all proxy traffic with current TLS standards. Furthermore, you may enforce multi-factor authentication for proxy administration portals. This may help to prevent credential compromise.
You may adopt a “minimal logging” policy. That is, log only essential metadata (e.g., timestamps, IP allocations). Purge logs regularly to meet data protection regulations. These might be GDPR, CCPA, or other data-protection rules.
Monitoring and Maintenance
To keep tabs on the efficacy of your implementation approach, you must track the following key metrics:
- Uptime/downtime reports:Compare actual availability against provider SLAs.
- Latency and throughput: Measure round-trip times and request volumes to detect bottlenecks.
- Error rates: Monitor HTTP response codes and connection handshake failures.
Automated Health Checks and Alerts
It’s best to integrate monitoring tools. These tools may execute periodic health probes against each proxy endpoint. Also, configure alerting rules that notify operations teams of anomalies. It may be via messaging platforms. The anomalies may be sustained packet loss or elevated error rates.
Conclusion
Optimizing your access control with ISP proxy infrastructure helps you save both time and money. It ensures fast, consistent, and resilient connections through ISP-provided IP addresses. Don’t settle for patchwork solutions — invest in ISP proxies and take control of your performance, privacy, and operational efficiency.